When the front door is intact and the foundation gives way, the lesson stops being about phishing.
When the front door is intact and the foundation gives way, the lesson stops being about phishing.
Schools are pulling Canvas offline as finals week begins. Not because of a phishing campaign. Not because someone clicked a bad link. Because ShinyHunters found a way through the ’Free-For-Teacher’ tier of Instructure's production infrastructure and used it to reach data that should have been nowhere near it. The result, according to ShinyHunters' own claims, is 3.65 terabytes of data and around 275 million records pulled from nearly 9,000 institutions, including Duke, Penn and Harvard.
This breach reads differently from almost everything else ShinyHunters has done in the last twelve months. It should change how security teams think about multi-tenant SaaS risk.
Why is this Canvas breach different from typical ShinyHunters attacks?
Most of the headline ShinyHunters campaigns in 2024 and 2025 leaned on social engineering: OAuth abuse, voice-phished session tokens, stolen credentials from Snowflake and Salesloft customers. All of them worked because identity was the soft target.
The Canvas incident appears to be something else. Early reporting from Rescana, Bitdefender and others points to an exploitation of the Free-For-Teacher account program, a low-friction signup tier that ran on the same production Canvas infrastructure as paid enterprise tenants. Instructure hasn't published a technical postmortem yet, but the early picture is consistent: this was a platform-level entry point, not a phished employee. That makes it one of the rare ShinyHunters breaches where the attacker didn't need to fool anyone. They just needed an architectural seam.
That distinction matters. Phishing breaches are stories about people. This one is a story about trust boundaries that weren't drawn correctly in the first place.
What does the blast radius say about lateral movement?
The scope is staggering. Names, email addresses, student IDs and private student-teacher messages were exposed. Reporting suggests source code and internal records were in scope too. When a single foothold reaches code, records and message history across thousands of tenants, the isolation model itself has failed. Containment was never on the table.
The principle CISOs already know is the one being underlined here. Least privilege isn't a checklist item. It's a blast-radius calculator. The smaller the trust each identity, service or tenant carries, the fewer escalation paths an intruder finds when they're already inside. The lateral movement through Canvas looks wide and sweeping for exactly the opposite reason: the privilege model assumed too much.
What should institutions worry about after Canvas comes back online?
Restoration won't close this out. Recovery is a separate problem with its own clock.
Two things deserve disproportionate attention in recovery. First, the risk of bombs left behind. An attacker who held this level of access for a week likely planted persistence: dormant accounts, modified course content, altered grades, injected scripts or seeded backdoors that survive a patch cycle. Schools that flip Canvas back on without forensic review are inheriting whatever the attacker left.
Second, data integrity. Confidentiality is the headline loss. Integrity is the quieter one. Did anyone modify records, transcripts or assignment data while they had the run of the platform? At the end of a term, that matters in ways that ripple for years.
And it goes without saying that Canvas should resolve the open issues that allowed a ‘free’ account to run on the same underlying infrastructure as the ‘enterprise’ tier and that more robust controls exist between tenants.
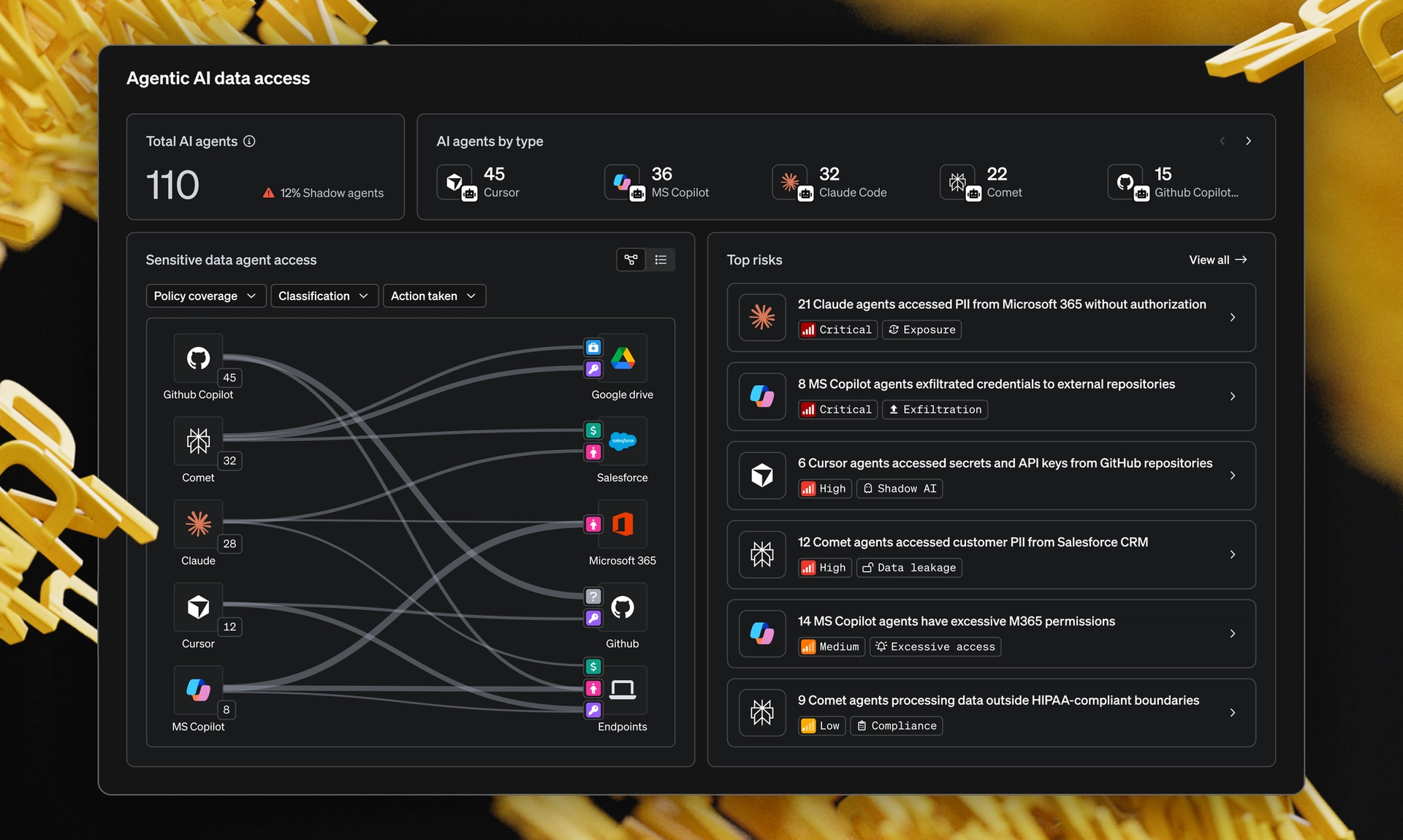
How does this change the way security teams think about SaaS?
For CISOs, the takeaway from the ShinyHunters Canvas breach is more uncomfortable than "audit your Canvas tenant." Every SaaS platform you depend on has a free tier, a partner integration, a developer sandbox or a low-friction account type that runs on shared infrastructure with your production data. Each one is a candidate for the same failure mode.
The defense is foresight. Know where your sensitive data lives across SaaS and which identities and services can reach it. Watch what moves, when it moves and in what context. Perimeter thinking won't cover this. The exposure now sits in the data layer.
This is where MIND comes in. We aren't just classifying files or counting matches. We're minding the data itself: where it sits, how it moves between SaaS apps and which context around a movement should make a security team pay attention. When the platform you trust breaks its own isolation model, the signal worth seeing lives in the data path, not at the login page.
If your institution is rebuilding from this breach or preparing for the next one, start with the question Canvas is answering the hard way: do you actually know what data was reachable and from where? See how MIND surfaces that picture in your own environment.
Let's mind what matters.